Many U.S. crypto traders assume account recovery is a simple fallback: lose a password, click “forgot,” and you’re back. That’s partly true for ordinary web services but misleading for exchanges that mix custodial and non-custodial features. OKX combines a centralized exchange with a self-custodial Web3 wallet and heavy regulatory controls. The sign-in and verification choices you make determine what you can recover, what you must secure yourself, and how much risk you accept.
This article compares two common sign-in and custody patterns on OKX — full custodial accounts (CEX sign-in with KYC and platform custody) versus self-custodial Web3 wallet access — and explains the security trade-offs, operational behaviors, and verification steps (KYC) that matter for U.S.-based traders. It emphasizes mechanisms: how enrollment, two-factor authentication, and identity checks reduce attack surfaces, where they fail, and what to watch next.
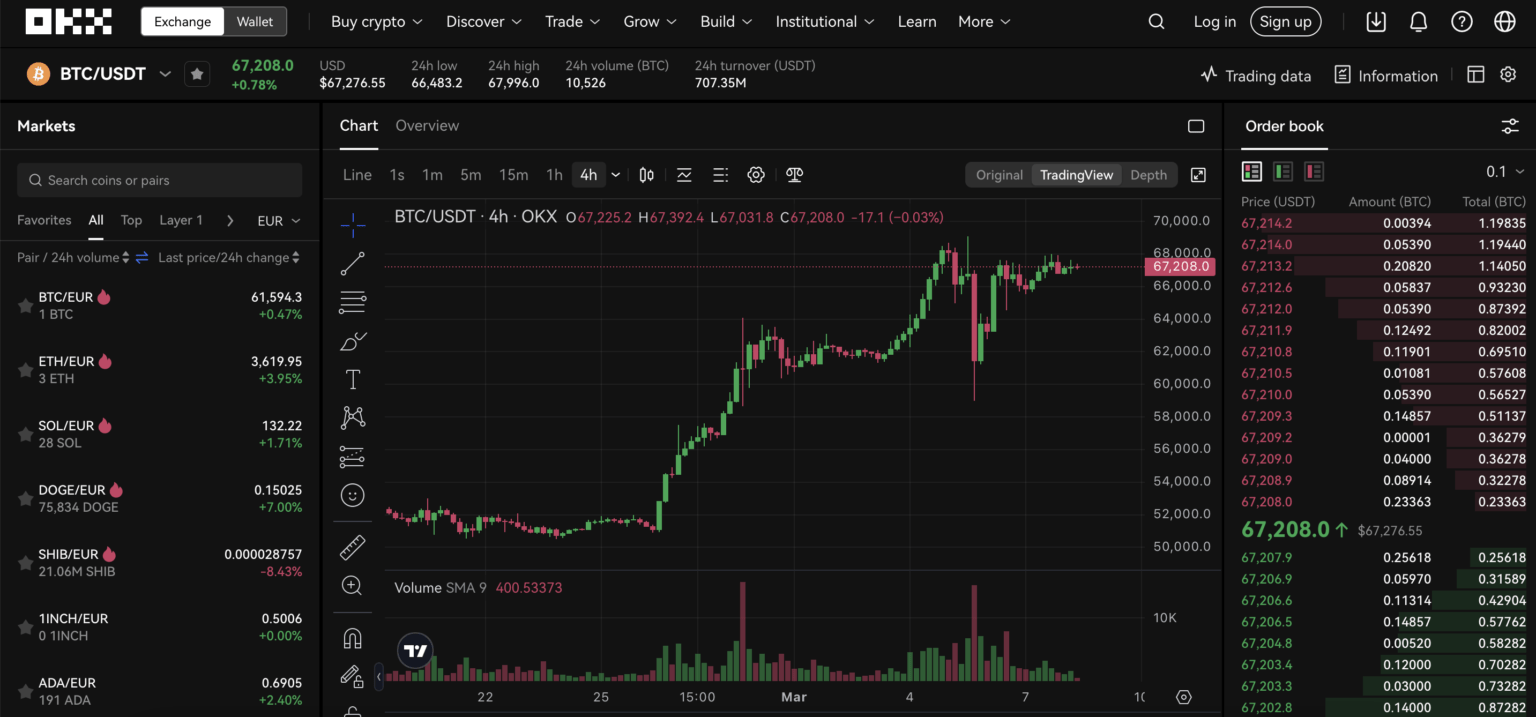
Two routes to access OKX: custodial CEX account vs non-custodial Web3 wallet
Mechanically, an OKX account can be thought of as one of two distinct sessions: (A) a custodial CEX account where OKX holds your deposited crypto and enforces AML/KYC; and (B) a self-custodial Web3 wallet where you control private keys and sign transactions locally. The two look similar on the surface — same app, same portfolio tab — but they create different threat models.
Custodial flow: you register with an email or phone, submit government ID and a live facial check (KYC), and enable mandatory 2FA. OKX then places most assets (>95%) in multi-signature cold storage and provides on-chain Proof of Reserves that let you audit backing but not individual keys. Recovery here is operationally possible but gated: account locks, legal requests, or supply-chain compromises can slow or block access.
Non-custodial flow: you create or import a seed phrase, optionally connect a hardware wallet (Ledger/Trezor), and transact by signing locally. OKX’s Web3 wallet is merely an interface; if you lose the seed phrase, there is no central recovery. That’s simple custody truth: self-custody buys control and forfeits centralized recovery.
Sign-in mechanics, verification, and the attack surfaces they change
Understanding the mechanical pieces clarifies where security actually lives. Key elements are: credentials (passwords), identity verification (KYC), two-factor authentication (2FA), device trust/bios (biometrics), and seed phrase or hardware keys for Web3 wallets. Each element reduces certain risks and exposes others.
Passwords and KYC reduce anonymous theft and make fraudulent withdrawals harder because exchanges can freeze funds pending investigation. But KYC introduces privacy and operational risk: identity data can be phished or exposed, and compliance processes can be points of friction during urgent markets. Two-factor authentication (SMS, Authenticator apps, biometrics) significantly lowers account-takeover risk; however, SMS is weaker than an app or hardware-based 2FA because of SIM-swap attacks. Biometric logins on mobile are convenient but must pair with device-level protections and trusted enrollment to be effective.
For Web3 wallet users, the critical attack surface is seed phrase theft and malicious DApp approvals. Browser extensions and mobile connectors enable interaction with thousands of DApps but also open phishing and contract-exploit vectors. Hardware wallets reduce this surface by moving the signing operation into a tamper-resistant device; they are not invulnerable, but they change the class of attack you must defend against.
Account verification (KYC) — how it helps and where it limits you
OKX’s KYC requirement in the U.S. involves government ID submission and a facial liveness check. Mechanistically, this is intended to tie account credentials to a real person and satisfy AML rules. Practically, KYC can reduce certain scams (e.g., money-mule scams) and provides legal recourse if illicit transfers are involved. It also enables full-featured trading: higher deposit/withdrawal limits, derivatives access, and fiat on/off ramps.
Limitations: KYC is not a panacea against phishing or credential stuffing. Fraudsters who successfully social-engineer or compromise a device can still perform authorized actions under a verified account. KYC also creates single points of exposure — identity documents and liveness checks — which attackers value. In short: KYC shifts the failure modes from anonymity-based fraud to identity-exposure incidents.
Practical trade-offs — when to pick custodial vs non-custodial access
If you are an active U.S. trader aiming to use spot, margin, or derivatives (up to 125x on some products), custodial access with KYC is the operationally sensible choice because it gives liquidity, leverage, and fiat rails. You gain compliance protections and the ability to recover access through the exchange in many situations — but you must accept that OKX has custodial control over deposited funds and that identity documents are stored somewhere in OKX’s systems.
If you prioritize absolute control over keys, want to interact with DeFi DApps or the OKX DEX aggregator, and are comfortable with irreversible backup responsibilities, use the non-custodial wallet and hardware keys. This path reduces centralization risk (no exchange freeze) but introduces permanent-loss risk if the seed is lost — a classical custody trade-off.
Heuristic: treat custodial accounts as operational trading accounts and non-custodial wallets as longer-term or protocol-interaction vaults. For many traders, a hybrid approach is best: keep active trading balances on the custodial side (with strict 2FA and device hygiene) and move larger reserves to a hardware-protected self-custody wallet for long-term holding or DeFi experiments.
Sign-in checklist for U.S. OKX users — what to do before you trade
1) Use a password manager and a strong unique password. 2) Prefer an authenticator app or hardware 2FA over SMS. 3) Enroll device biometrics only if your device has full-disk encryption and you understand the recovery implications. 4) Complete KYC when you need higher limits or derivatives, but avoid uploading sensitive ID images from insecure networks. 5) For Web3 wallet use, write the seed phrase on paper (not cloud) and consider a hardware wallet for any balance you cannot afford to lose. 6) Monitor Proof of Reserves and platform announcements; routine delistings or liquidity shifts change which assets are safe to hold on-platform.
These steps map to clear mechanisms: make credential compromise harder (passwords + 2FA), make device compromise less valuable (biometrics + encryption), and limit irreversible loss (hardware wallets + cold storage for long-term funds).
Where sign-in and verification break in real situations — three failure modes
1) Phishing + social engineering: attackers mimic OKX interfaces to capture credentials and 2FA codes. Even strong passwords fail when users approve malicious transactions. Defense: never paste seed phrases; verify domain names; use hardware wallets.
2) SIM-swap & device compromise: SMS-based 2FA and lost/reused passwords can let attackers pass KYC challenge flows. Defense: avoid SMS 2FA; vendor SIM-lock services and port-out alerts help at the carrier level.
3) Regulatory or operational freezes: a verified custodial account can be frozen during investigations or under regulatory pressure, blocking withdrawals even to verified owners temporarily. Defense: diversify custody — keep working funds on-platform and reserves off-platform.
Short near-term signals to watch (conditional scenarios)
Keep an eye on two things that will affect how you should sign in and verify: (a) changes in AML/KYC rules and enforcement in the U.S., which could tighten identity requirements and make custodial recovery slower; and (b) ecosystem-level security incidents (smart contract exploits or exchange hacks) that shift risk premiums toward self-custody. If regulators increase documentary requirements, expect longer KYC processing times and possibly stricter device verification. If cross-chain DEX exploits spike, you should tighten approval habits and favor hardware signing when interacting with unknown contracts.
If you want a quick entry point for signing in on the web, use the official login flow and check the URL carefully; a reliable starting page is here: okx login.
FAQ — quick answers to common sign-in and verification questions
Q: If I complete KYC on OKX, can I always recover my account?
A: KYC improves the odds of recovery because the exchange can verify identity, but it is not a guarantee. Recovery can be delayed or blocked by legal holds, fraud investigations, or if an attacker also controls devices or email. KYC reduces anonymity-based fraud but creates other privacy exposures.
Q: Is SMS-based 2FA acceptable for OKX sign-ins in the U.S.?
A: It is better than no 2FA but weaker than an authenticator app or hardware key because SIM-swap attacks are a known risk. For trading accounts with significant balances or derivatives access, prefer app-based 2FA or hardware-backed methods.
Q: Can I use the same OKX credentials for the Web3 wallet and the centralized exchange?
A: The interfaces are integrated, but custody differs. You can use one app for both, yet the Web3 wallet controls private keys independently. Treat the wallet seed as a separate, high-security secret even if you access it from the same device.
Q: What should I do immediately after signing in on a new device?
A: Enable 2FA, confirm withdrawal whitelist settings, avoid approving unknown DApp connections, and move large balances to hardware or cold storage if you plan to hold longer term. Validate device security: full-disk encryption, OS updates, and a reputable anti-malware posture.

